SPECIAL REPORT: Police Pre-Crime Algorithm Uses Social Media Posts Against You in Real Time
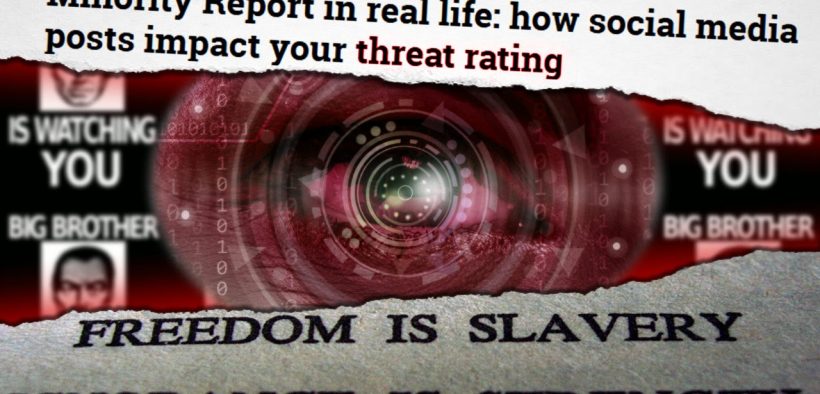
We have finally reached the moment where Orwell’s nightmare in 1984 meets the film Minority Report. We’re living there right now.
And, astoundingly, we still hear people saying “Well, I haven’t done anything wrong, so I don’t have anything to worry about.”
Trending in the world of tomorrow is pre-crime “predictive policing,” which uses vast Big Data stores to compile profiles on the citizenry, allowing law enforcement and government officials to hone in on targets, with promises of predicting where crimes will happen next, and preparing for encounters with individuals who have been assessed as high risks.
Welcome to the ill-conceived Orwellian-era of “Big Data”-enhanced intelligence-led integrated policing which compiles records from private, consumer, government and social media sector create a pre-crime threat assessment that determines how police will handle you and whether you will be suspected before even doing anything wrong.
Wow! That’s a mouthful of terms.
But it’s true. This technology has already been put into the hands of police across the country.
Private sector surveys have found that 83% of law enforcement now use social media in conducting investigations, while social media data that has been used for probable cause in warrants has been upheld by courts 87% of the time when challenged.
For most, social media fits into the investigation through the use of predictive policing software, such as the “Beware” system sold by Intrado, who operate the nationwide 9-1-1 emergency communications system used by police and first responders in every case. As the Examiner reported:
Your local police department is likely using numerous tools and applications that might determine how you get treated during a routine traffic stop, or in response to your neighbor’s call about loud music. One such application, Beware, has been sold to police departments since 2012. It can be accessed on any Internet-enabled device, including tablets, smartphones, laptop and desktop computers, while responders are en route to, or at the location of a call.
This app explores billions of records in social media postings, commercial and public databases for law enforcement needs, churning out “risk profiles” in real time. ‘Beware’ algorithm assigns a score and “threat rating” to a person — green, yellow or red – and sends that rating to a requesting officer. Worst of all, this information is not made available to the very person whose “threat rating” is being appraised. You have no ability to dispute being wrongly designated a high-risk potential offender.
For example, you wrote something about recent Ferguson protests on Facebook. Perhaps, you expressed dissatisfaction with police brutality. Maybe you complained about the CIA’s torture tactics, demanded President Obama’s impeachment or criticized the government in general. You could have shared a petition for the preservation of gun rights, or bought a holster online. You could also be mistaken for another person with a criminal record or a history of radical Internet postings. It could mean the difference between waltzing off with a warning, or being subjected to a brutal takedown at gun point. It could turn a simple knock at the door into a full-blown SWAT raid.
Not even a joke.
All the makings are here for targeting political activists, flushing out dissidents, catching debtors for the benefit of their creditors, and branding groups of all political stripes with dangerous and undue labels such as “potential domestic terrorists,” “unruly mobs, etc.” and labeling rogue individuals as “lone wolves.” These cases focus on the potential threat of errant behavior or offensive actions as justification to monitor, target and assessment, rather than actual criminal records used in past criminal databases.
The slippery slope of potential abuse appears so slippery and so sloped that it is a nearly vertical slide to total centralized power.
Reuters reported some other predictive policing services, too, including the government sanctioned FirstNet system that will connect all first responder calls and database assessments nationwide on a wireless broadband network. Known to some as 9-1-1 2.0, this system works a private-public partnership, which for-profit corporations facilitating the agendas of law enforcement:
New World Systems, for example, now offers software that allows dispatchers to enter in a person’s name to see if they’ve had contact with the police before. Provided crime data, PredPol claims on its website that its software “forecasts highest risk times and places for future crimes.” These and other technologies are supplanting and enhancing traditional police work.
Public safety organizations, using federal funding, are set to begin building a $7-billion nationwide first-responder wireless network, called FirstNet. Money is now being set aside. With this network, information-sharing capabilities and federal-state coordination will likely grow substantially. Some uses of FirstNet will improve traditional services like 911 dispatches. Other law enforcement uses aren’t as pedestrian, however.
These systems put incredible power in the hands of law enforcement officers, and stand to color their judgement of individuals they are supposed to treat equally with due process under the law.
Instead, circumstantial evidence is used to imply guilt by association, trend, and pattern opening the door widely for abuse and preferential treatment. The stuff that has happened in places like Ferguson, New York, Cincinnati, Albuquerque and elsewhere may be nothing compared to what could happen with this type of leading and proprietary information.
Individuals, who may be targeted by this system and assessed as a threat, have no way of knowing what has been claimed against them. There is no venue for facing their accuser; instead, it is a whisper campaign coordinated between the most powerful corporations and banks, who’ve collected private intelligence on their customers, the police and public, government held records and a compilation of social media “events” that may or may not represent the intentions of people under the spotlight.
The City Council in Bellingham, Washington state have the distinction of being the only locale to challenge the encroaching adoption of Intrado’s Beware database software. After significant outrage by its citizens deeply concerned about the privacy implications of the program, its council members acknowledged the fact that its own authority as a city would not allow it to know what data is being collected, considered and used by its police department.
“Given that this is a private company, they are not subject to the same public records act that government agencies are subject to, so unless the company is forced to give this information to the City Council as part of the buying process now being considered, we may never know how these threat scores are developed,” Hildes said.
“We do know that Intrado’s threat score is partially based on social media statements. If someone has made any threatening statements on the internet, that goes into the score. But who knows how much weight is given to this? So someone who rails against the government or against police abuse, can they expect that if they call 911 or someone calls 911 about them, that they will be facing guns drawn because of the Intrado score?”
Ultimately, the city refused the police software on budgetary grounds… for now.
However, Bellingham, like most cities, is being offered “Beware” software with the enticement of federal grant money urging easy adoption. That means most every other city, county and state law enforcement agency is taking the bait and implementing a troubling, invasive and downright dangerous crime screening program that is making the surveillance society and police state much, much worse very quickly.
You have been warned… Big Brother is real, Big Bro is here
Don’t say you weren’t warned, because George Orwell a.k.a. Eric Blair totally did, along with many others. Weren’t you paying attention? Orwell foresaw a Big Brother society of total surveillance and repressive control, but that was just the beginnings of this tyranny.
Today, with a better understanding of how the Internet is capable of transforming our lives, our economy and our society, we are poised to enter the era of the “smart society” where “Big Data” is collected in literally every facet of your life and shared over the “smart grid” with law enforcement, utility companies and other relevant stakeholders – everything from when you use your appliances, to when you drive your car, when you cook breakfast, what you throw away in the trash to of course what’s in your bank account and what you view online.
2013, the Year of the Edward Snowden Leaks, the mass surveillance program of the NSA and its partners into the limelight.
Yet, these programs and actions like them have not been stopped, reigned in, checked or even buried in the underground of secret government activity.
They continue and get worse and worse with each passing day. These abuses are totally allowed by the system. OK?
Instead, the shocking admissions of ubiquitous government spying on its citizens (in the name of protecting them from terrorists, no less) has been a big coming out party!
Here’s just some of what we know about:
A Very Long Train of Surveillance Abuses in Just a Few Short Years
• Fusion Centers established by the Department of Homeland Security and the FBI have been set up at 78 locations across the country, concentrating a new policing attitude in big urban areas in the paranoid decade that followed 9/11. It was the launch of “pre-crime” data-driven “intelligence-led policing” to the local law enforcement level.
Authorities across all jurisdictions combine data from public and private sources to create “actionable intelligence” and assess threats of targets, including those who’ve not been suspected of committing a crime. This spying on citizens for potential crimes includes active monitoring of activists, dissidents and political and community groups – raising concern in all who are paying attention… even if they “aren’t doing anything wrong.”
As the Electronic Frontier Foundation explains,
”Fusion centers are a local arm of the so-called “intelligence community,” the 17 intelligence agencies coordinated by the National Counterterrorism Center (NCTC). The government documentation around fusion centers is entirely focused on breaking down barriers between the various government agencies that collect and maintain criminal intelligence information.”
Sgt. David Lambert, of the Massachusetts State Police Commonwealth Fusion Center defines “data fusion” as “the exchange of information from different sources—including law enforcement, public safety, and the private sector—and, with analysis, can result in meaningful and actionable intelligence and information” that can inform both policy and tactical deployment of resources.”
• Potential Domestic Terrorists and Clever, Kinetic Homeland Defense: Homeland Security issued a memo in 2009 warning that returning veterans, constitutionalists, Tea Party members, “left wing” and animal rights groups and others could be potential domestic terrorists. Similar memorandums issued by federal agencies and state and local law enforcement groups express similar threat assessments, however misguided and baseless.
This severe designation – identified as being a possible terrorist – serves as a Scarlet Letter to bring undue scrutiny of these groups, who are primarily engaged in free speech activities protected under the 1st Amendment. These and other groups are subject to monitoring, investigation and even potential indefinite detention under the NDAA simply due to their political affiliations and philosophies.
• As the New American notes,
“A 2009 report by the Missouri Information Analysis Center labeled those who have bumper stickers for third-party political candidates such as Ron Paul, Bob Barr, and Chuck Baldwin as suspicious individuals. It further warned law enforcement to watch out for individuals with “radical” ideologies based on Christian views, such as opposing illegal immigration, abortion, and federal taxes.”
• In 2005, police investigators were using GPS tracking darts attached to the vehicles of a suspected drug kingpin to conduct extensive surveillance under a court issued warrant. The Supreme Court slapped down the use of this privacy invading technique in 2012, but only objected to the long-term use of the GPS tracker over the course of more than a one month period. It was a hailed a landmark decision protecting privacy – yet no meaningful protections exist in this now brazenly post-Constitutional technologically-driven world.
• The use of Sting Ray technology – a data interceptor program that forces cell phones into sharing data by imitating cell towers used by the FBI, local law enforcement and likely other entities including the military, the NSA and foreign government intelligence agencies – has been exposed little by little, and court challenge of its anti-Constitutional activities has yet to take place.
The Electronic Frontier Foundation described its capabilities this way:
A Stingray works by masquerading as a cell phone tower—to which your mobile phone sends signals to every 7 to 15 seconds whether you are on a call or not— and tricks your phone into connecting to it. As a result, the government can figure out who, when and to where you are calling, the precise location of every device within the range, and with some devices, even capture the content of your conversations.
The feds are paying for local police to obtain the devices:
High levels of secrecy and rumors about the Stingray’s power, though, have contributed to a lingering curiosity about the surveillance technology. Known throughout the law enforcement community as an International Mobile Subscriber Identity catcher, the Stingray is a suitcase-sized metal box that’s typically transported in the back of police vehicles. Harris Corp. charges as much as $400,000 for each device, with the federal government footing the bill for local police departments who say they should be given a Stingray to investigate potential terrorists in their area.
At least 43 police agencies in 18 states have Stingrays, using them for a variety of criminal investigations ranging from drugs to violent offenses, with a police spokesman in Georgia saying in July that it’s used “in criminal investigations with no restrictions on the type of crime.” Before that, the ACLU said, the U.S. Marshals Service conspired with local police in Florida to mislead a judge about the Stingray’s technical capabilities.
• It was revealed that the Justice Department is secretly flying small aircraft over major cities to scoop up cell data using a related cell phone interceptor technology known as “dirtboxes”:
The Justice Department is scooping up data from thousands of mobile phones through devices deployed on airplanes that mimic cellphone towers, a high-tech hunt for criminal suspects that is snagging a large number of innocent Americans, according to people familiar with the operations.
The U.S. Marshals Service program, which became fully functional around 2007, operates Cessna aircraft from at least five metropolitan-area airports, with a flying range covering most of the U.S. population, according to people familiar with the program.
The technology in the two-foot-square device enables investigators to scoop data from tens of thousands of cellphones in a single flight, collecting their identifying information and general location, these people said.
• Piece by piece, also comes to light through the Snowden PRISM leaks that all the major telecoms and social media firms have willingly shared data with the NSA and other government and law enforcement agencies. The NSA tapped user data and telephone records from companies including Apple, Google, Verizon and Microsoft.
Ostensibly, these tech giants called upon governments to stop spying on their respective customers and citizens, and to reign in data collection. No such reform takes place, however, as numerous other forms of data collection, location monitoring and records sharing come to light. After a while, it is no longer funny or surprising. Least of all shocking.
• Facebook, Twitter, LinkedIn, Pinterest, Google+, Tumblr, Instagram, flickr and other platforms become the commons of the 21st Century, and along with its corners, nooks and crannies for every personality, storing vast amounts of traceable data including identity, photos and facial features, location, interests, employment, associates and a voluntary list of taboo behaviors, all of which can be analyzed and integrated by law enforcement, intelligence and data specialists. The Onion said it best:
•“Selfie” is officially entered the Oxford dictionary in 2013, and became a standard activity by the hoards of self-interested people “living in public” in the online realm of social media.
• Smart Phones go from being very popular to never left behind… by almost anyone. People of all ages and walks of life find these mini-computer communication devices indispensable – and frankly addictive. They broadcast endless bits of data through conversation, texts, location data (GPS triangulated), photos, video, login and user information, Internet searches, apps and more.
• “Wearables” stand poised to displace the Smart Phone trend, linking the mini-computer communicator and tracker more closely than ever to the intimate lives of individuals. Smart wristwatches, glasses and exercise/training/monitoring dongles are collecting and keeping tabs and stats about physical movements, heart rate, sleep patterns, schedules, surroundings and plenty of other categories, all of which can be networked online and charted against other members of the group and general population. As TIME magazine notes, tech giants from Silicon Valley have “redrawn the line that separates our technology and ourselves.”
It is the age of “sousveillance,” where surveillance is enhanced by the participation of the subjected.
Sousveillance is the recording of an activity by a participant in the activity typically by way of small wearable or portable personal technologies.
• (Oh, and it is more clear than ever that Google is much more than a search engine and advertising giant… it is an aspiring god with a strong inclination for omniscience and the potential for omnipresence and perhaps even omnipotence. A vision of transcendent collective intelligence is no longer a pipe dream; privacy becomes not only violated and backseated, and not only dead, but privacy becomes a sin under the paradigm of “total information awareness.”
• Since 2008, the secretive Bilderberg meetings, where the elite controllers of banking, industry, politics, the military industrial complex and academia converge, has discussed aspects of the newly-dubbed Cyberwar, inviting Gen. Keith Alexander, then simultaneous director of the NSA, the Central Security Service and USCYBERCOM, and numerous IT and Internet entrepreneurs and data experts based in Silicon Valley over the prevailing years. Among these are executives from Google, Facebook, Microsoft, PayPal, Amazon.com, LinkedIn, Twitter, TomTom and the controversial NSA-contracting firm Palantir.
• The Cyberwar front of military conflict, which engages foreign states, terrorists and rogue targets with online attacks, now effectively takes aim at the activities of domestic, civilian populations in everyday life, consumer purchasing and especially in social media interactions.
• In 2012, the NSA unveils its massive data hub in the Utah desert, capable of storing seemingly limitless quantities of information collected through mass surveillance programs. Its status as a rogue, para-government monster seems conspicuously obvious.
• At its 2013 meeting, Bilderberg effectively announced that “Big Data is changing almost everything,” discussing a juncture where private sector and consumer data had become so pervasive as to render mass surveillance inevitable, ubiquitous and incredibly pervasive in so many areas of life.
Special Report: How Bilderberg Will Use Technology to Rule by 2050
Less than a week after this secret meetings at Bilderberg, Edward Snowden brought forward his leaks on NSA and contractor spying activities under the PRISM program, later revealing hundreds of other programs and data points on the vast cooperation of the telecomm and Internet industry in sharing unbelievable quantities data with the National Security Agency. These revelations are first published in the Washington Post, a paper connected for decades to the Bilderberg conference through its long time owner Katherine Graham and her son Donald Graham, both annual attendees.
• NSA director Gen. Keith Alexander resigns his longtime post in the wake of the Snowden leaks and mounting controversy… only to create a private advisory firm that keeps Wall Street abreast of cyber threats and consumer trends, with expertise and employees plucked from the NSA vaults of info-power. A serious debate over the revolving door and fascist relationship between private corporations, public government and the secret government seems non-existent.
• In the fall of 2013, Amazon.com founder Jeff Bezos, also a Bilderberg attendee, purchased the Washington Post. CIA contracts with Amazon.com bring controversy and closer scrutiny between the online world and its ties to the world of politics, media, power and clandestine government activities.
Who watches the watchers?
As Alan Moore, author of the graphic novel, made clear in his poignant The Watchmen, timepieces were made irrelevant with the advent of Einstein’s theory of relativity. Nuclear power and other breakthroughs were the future.
The vision for society is as broken as the scattered watch parts of the once watch-making father of the man who would become known as Dr. Manhattan, a superman born out of chance and the time where the military industrial complex, private interests like the Rockefeller Foundation and powerful scientific research converge.
And what of the future?
The future no longer belongs to the citizens of the United States or the peoples of the world.
That future has been stolen; the purpose and value of human labor and ingenuity has been debased again and again, as technology becomes our workers, servants, authorities and, indeed, our watchers.
Where things go from here are hard to define, but are less and less rooted in the traditions of individual liberty and self-sufficiency that has defined the American character and its unique pursuit of freedom.
Of course, all of this is blatantly unconstitutional, not that anyone in power in the 21st Century cares.
Members of law enforcement have literally been indoctrinated to think that the Constitution is a piece of history that ‘doesn’t much apply.’ I know, because I’ve been told directly from friends and family members who have worked in law enforcement.
Such tactics clearly infringe upon, or severely limit the protection in the Bill of Rights and the rights of all Americans under the intended system of limited government, separation of powers and due process under the rule of law.
And of the Constitution and Bill of Rights?
These protections have all but been destroyed, eroded, diluted and swept away. And it’s not just the 4th Amendment.
The 1st Amendment, which reads:
Congress shall make no law respecting an establishment of religion, or prohibiting the free exercise thereof; or abridging the freedom of speech, or of the press; or the right of the people peaceably to assemble, and to petition the government for a redress of grievances.
has been violated in numerous and often subtle ways through systematic cases of monitoring and surveillance of protestors. Their speech has been chilled by the acts of occupying police forces and terms branding them as potential criminal terrorists. Free speech zones and over zealous codes have limited the places and nature of assembly.
The press, in particular, has been restricted in the age of “big data” and mass surveillance. Investigative journalists and whistleblowers have been prosecuted, persecuted, slandered, jailed, tortured, spied upon and, in some cases, suffered untimely deaths. Examples of this include Bradley Manning, Jeremy Hammond, Barrett Brown, Andrew Breitbart, Michael Hastings, Glenn Greenwald and far too many others.
The 2nd Amendment, which reads:
A well regulated militia, being necessary to the security of a free state, the right of the people to keep and bear arms, shall not be infringed.
has been violated in numerous ways. Highly manipulated, high profile cases have led to unreasonable infringements upon the right to own firearms. Laws for background checks and other regulations have increased, while databases not only check applicants for criminal records, but store owner identification information. Increasingly, data surrounding gun owners and gun rights advocates is being assembled into a de facto gun registry, match against such databases as mental health screening, medical history and police intelligence threat assessments. Efforts to disarm and bar gun possession on the basis of new and expanding criteria is underway.
The 3rd Amendment, which reads:
No soldier shall, in time of peace be quartered in any house, without the consent of the owner, nor in time of war, but in a manner to be prescribed by law.
is less evident than many violated rights, but effectively nullified by a permanent standing Armed Forces and a growing police state compromised of various local, state and federal units armed with the weapons of war and willing to control populations with force.
Further, the invasion of our lives through data surveillance on numerous digital devices has in some ways effectively brought quartered troops and unannounced spies into every home, room and even individual body.
The 4th Amendment, which reads:
The right of the people to be secure in their persons, houses, papers, and effects, against unreasonable searches and seizures, shall not be violated, and no warrants shall issue, but upon probable cause, supported by oath or affirmation, and particularly describing the place to be searched, and the persons or things to be seized.
is the most widely recognized for its complex array of violations. TSA inspections at airports broke down Americans to accept prison conditions, where all persons and possessions are searched, and items seized without warrant or probably cause.
The unauthorized collection of mass communications data by the NSA is an astounding and ongoing violation of all these principles as well. Moreover, through Sting Ray and other programs, the FBI and local police are engaged in these data sweeps as well.
No American alive today is even remotely secure in their persons, houses, papers or effects. Period. Even members of Congress were illegitimately spied upon.
The 5th Amendment, which reads:
No person shall be held to answer for a capital, or otherwise infamous crime, unless on a presentment or indictment of a grand jury, except in cases arising in the land or naval forces, or in the militia, when in actual service in time of war or public danger; nor shall any person be subject for the same offense to be twice put in jeopardy of life or limb; nor shall be compelled in any criminal case to be a witness against himself, nor be deprived of life, liberty, or property, without due process of law; nor shall private property be taken for public use, without just compensation.
describes just some of the massive violations underway to deny due process of law in the proceedings of the surveillance state. Through ongoing mass surveillance and accessing profiles and threat assessments of individuals, the data surrounding one’s life makes it difficult if not impossible to witness against himself. Use of civil asset forfeiture by police and federal authorities, emboldened by extrajudicial data collection and digital investigations, amounts to a shameful breach of the 5th Amendment that has provided millions upon millions of dollars in illegitimate assets to the state coffers.
The 6th Amendment, which reads:
In all criminal prosecutions, the accused shall enjoy the right to a speedy and public trial, by an impartial jury of the state and district wherein the crime shall have been committed, which district shall have been previously ascertained by law, and to be informed of the nature and cause of the accusation; to be confronted with the witnesses against him; to have compulsory process for obtaining witnesses in his favor, and to have the assistance of counsel for his defense.
has been degraded through the procedures of deals cut between prosecutors, the insanely high conviction rates in court and through other color of law actions to shortcut due process and intimidate suspects into submitting to imprisonment, fines and fees without a true day in court or burden of proof against him.
Red light cameras, often combined with shortened traffic signal times, have become a particularly odorous example, with photographic evidence replacing the presence of a sworn officer, and a streamlined, corporatized revenue collection process set up to replace due process of law or accountable standards of public safety.
The 7th Amendment, which reads:
In suits at common law, where the value in controversy shall exceed twenty dollars, the right of trial by jury shall be preserved, and no fact tried by a jury, shall be otherwise reexamined in any court of the United States, than according to the rules of the common law.
has also been violated in many cases, and further attests the tipping of the scales of justice towards revenue collection-oriented prosecution, where guilty pleas are often induced or incentivized, while trials and due process have been discouraged. The automation and speed of data and digital platforms of justice have exacerbated these tendencies.
The 8th Amendment, which reads:
Excessive bail shall not be required, nor excessive fines imposed, nor cruel and unusual punishments inflicted.
is a bit of a joke when one considers that the United States of America has become the global sponsor of torture as a means of getting confession, a nation that fails to indict or hold accountable officers of the law who unjustly kill its citizens or use excessive force, and who have sworn officers that frequently eat out the substance of its people through fines and fees for every petty offense, and a labyrinth of costly legal ramifications for every more serious offense.
The 9th and 10th Amendments, often analyzed as a pair reminding The People of the restraints intended on the federal government, and of the abundant rights the people, read:
The enumeration in the Constitution, of certain rights, shall not be construed to deny or disparage others retained by the people.
and
The powers not delegated to the United States by the Constitution, nor prohibited by it to the states, are reserved to the states respectively, or to the people.
These too have been violated. Federal agencies under the executive branch have drastically overstepped the bounds of the Constitution, and have used federal grant making power – derived from the burdensome taxation of The People – to control the several states and the many counties, cities and towns. In turn, unconstitutional and odorous policies of all kinds are imposed, altering the intentions and due diligence of many areas, including law enforcement, local government, education, travel (driving, etc.), commerce and more.
Meanwhile, the rights of The People have been trampled upon by all levels of government, with contempt and mockery when these rights are expressed and defended. Libelous and slanderous tones are used by agencies at the federal, state and local levels to disenfranchise and delegitimize true citizen activism. Compliance alone – compliance with each and every petty law and regulation – is truly tolerated. Predatory financial institutions have exploited these people in their affairs and attempt to survive and thrive, while government agencies have protected and enabled their actions, to the detriment of the rights and liberties of The People.
The world, boldly altered from its state of affairs by the American Revolution and Declaration of Independence against the long train of abuses by the British empire, has been turned flatly on its end.
None of these most enshrined rights have been sufficiently respected, and for some time now.
Unfortunately, the path we are following does not lead to freedom, liberty or individual self-worth.
It is a collective future. A fascist future. A corporatist future. A Sci-Tech dictatorship. A transcendent vision of perfectionism.
In fact, call it whatever you want. Just don’t be deceived into believing any of it is ultimately in your interest.